Merci, tiens-moi informé, car je suis bloqué pour la suite.
Wireguard + adguard + unbound + cloudflared = DoT / DoH !
Merci, je regarde ça demain.
Petit problème, lors du restart du service
service unbound restart
J'ai cette belle erreur, une idée ?
Job for unbound.service failed because the control process exited with error code.
See "systemctl status unbound.service" and "journalctl -xe" for details.
- Modifié
J'ai toujours l'erreur ci-dessus concernant unbound mais je peux quand même me connecter.
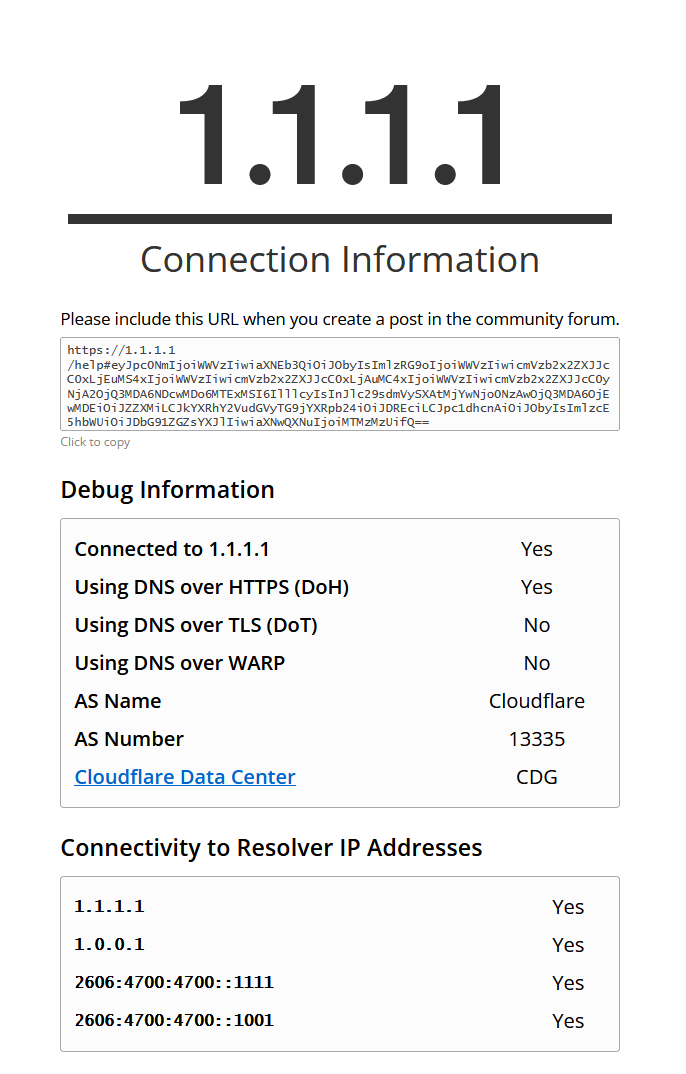
Et j'obtiens ceci via https://1.1.1.1/help. Je ne sais pas si c'est bon ?
- retour de la commande
dig -t -A google.fr ;; Warning, ignoring invalid type -A ; <<>> DiG 9.16.22-Debian <<>> -t -A google.fr ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 10058 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 1232 ;; QUESTION SECTION: ;google.fr. IN A ;; ANSWER SECTION: google.fr. 45 IN A 142.250.178.131 ;; Query time: 0 msec ;; SERVER: 2001:41d0:3:163::1#53(2001:41d0:3:163::1) ;; WHEN: Thu Mar 10 16:44:20 CET 2022 ;; MSG SIZE rcvd: 54
- Modifié
● unbound.service - Unbound DNS server
Loaded: loaded (/lib/systemd/system/unbound.service; enabled; vendor prese>
Active: failed (Result: exit-code) since Thu 2022-03-10 16:36:00 CET; 3h 5>
Docs: man:unbound(8)
Process: 1032970 ExecStartPre=/usr/lib/unbound/package-helper chroot_setup >
Process: 1032973 ExecStartPre=/usr/lib/unbound/package-helper root_trust_an>
Process: 1032976 ExecStart=/usr/sbin/unbound -d -p $DAEMON_OPTS (code=exite>
Process: 1032977 ExecStopPost=/usr/lib/unbound/package-helper chroot_teardo>
Main PID: 1032976 (code=exited, status=1/FAILURE)
CPU: 25ms
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Scheduled restart job, re>
Mar 10 16:36:00 ns336435 systemd[1]: Stopped Unbound DNS server.
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Start request repeated to>
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Failed with result 'exit->
Mar 10 16:36:00 ns336435 systemd[1]: Failed to start Unbound DNS server.
lines 1-16/16 (END)...skipping...
● unbound.service - Unbound DNS server
Loaded: loaded (/lib/systemd/system/unbound.service; enabled; vendor preset: enabled)
Active: failed (Result: exit-code) since Thu 2022-03-10 16:36:00 CET; 3h 51min ago
Docs: man:unbound(8)
Process: 1032970 ExecStartPre=/usr/lib/unbound/package-helper chroot_setup (code=exited, status=1/FAILURE)
Process: 1032973 ExecStartPre=/usr/lib/unbound/package-helper root_trust_anchor_update (code=exited, status=1/FAILURE)
Process: 1032976 ExecStart=/usr/sbin/unbound -d -p $DAEMON_OPTS (code=exited, status=1/FAILURE)
Process: 1032977 ExecStopPost=/usr/lib/unbound/package-helper chroot_teardown (code=exited, status=1/FAILURE)
Main PID: 1032976 (code=exited, status=1/FAILURE)
CPU: 25ms
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Scheduled restart job, restart counter is at 5.
Mar 10 16:36:00 ns336435 systemd[1]: Stopped Unbound DNS server.
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Start request repeated too quickly.
Mar 10 16:36:00 ns336435 systemd[1]: unbound.service: Failed with result 'exit-code'.
Mar 10 16:36:00 ns336435 systemd[1]: Failed to start Unbound DNS server.
Je pense que tu as du faire une erreur de copier coller dans le fichier
/etc/unbound/unbound.conf.d/unbound.confRegarde avec cette commande si les erreurs ressortent :
unbound-checkconf /etc/unbound/unbound.conf
- Modifié
MattProd Humm effectivement, le fichier est vierge, il me semblait l'avoir complété.
Suite à cela, voici ce qu'il en ressort.
[1646946753] unbound-checkconf[1043724:0] error: Could not open /etc/unbound/unbound.conf: No such file or directory
Pourtant le fichier doit être créer vers /etc/unbound/unbound.conf.d/unbound.conf et non pas /etc/unbound/unbound.conf
shiraz91 Parce que le fichier de conf générique créer par l'installateur est pourvu de cette facon :
# Unbound configuration file for Debian.
#
# See the unbound.conf(5) man page.
#
# See /usr/share/doc/unbound/examples/unbound.conf for a commented
# reference config file.
#
# The following line includes additional configuration files from the
# /etc/unbound/unbound.conf.d directory.
include-toplevel: "/etc/unbound/unbound.conf.d/*.conf"
Sur quel OS tu es ?
Mes tests et mon tuto sont réalises sous Debian 10 et 11
- Modifié
Dans :
/etc/unbound/unbound.confmet ça:
# Unbound configuration file for Debian.
#
# See the unbound.conf(5) man page.
#
# See /usr/share/doc/unbound/examples/unbound.conf for a commented
# reference config file.
#
# The following line includes additional configuration files from the
# /etc/unbound/unbound.conf.d directory.
include-toplevel: "/etc/unbound/unbound.conf.d/*.conf"
Et dans
/etc/unbound/unbound.conf.d/unbound.confAssure toi d'avoir :
server:
# The verbosity number, level 0 means no verbosity, only errors.
# Level 1 gives operational information. Level 2 gives detailed
# operational information. Level 3 gives query level information,
# output per query. Level 4 gives algorithm level information.
# Level 5 logs client identification for cache misses. Default is
# level 1.
verbosity: 0
interface: 127.0.0.1
port: 53
do-ip4: yes
do-udp: yes
do-tcp: yes
# May be set to yes if you have IPv6 connectivity
do-ip6: no
# You want to leave this to no unless you have *native* IPv6. With 6to4 and
# Terredo tunnels your web browser should favor IPv4 for the same reasons
prefer-ip6: no
# Use this only when you downloaded the list of primary root servers!
# Read the root hints from this file. Make sure to
# update root.hints evry 5-6 months.
root-hints: "/var/lib/unbound/root.hints"
# Trust glue only if it is within the servers authority
harden-glue: yes
# Ignore very large queries.
harden-large-queries: yes
# Require DNSSEC data for trust-anchored zones, if such data is absent, the zone becomes BOGUS
# If you want to disable DNSSEC, set harden-dnssec stripped: no
harden-dnssec-stripped: yes
# Number of bytes size to advertise as the EDNS reassembly buffer
# size. This is the value put into datagrams over UDP towards
# peers. The actual buffer size is determined by msg-buffer-size
# (both for TCP and UDP).
edns-buffer-size: 1232
# Rotates RRSet order in response (the pseudo-random
# number is taken from Ensure privacy of local IP
# ranges the query ID, for speed and thread safety).
# private-address: 192.168.0.0/16
rrset-roundrobin: yes
# Time to live minimum for RRsets and messages in the cache. If the minimum
# kicks in, the data is cached for longer than the domain owner intended,
# and thus less queries are made to look up the data. Zero makes sure the
# data in the cache is as the domain owner intended, higher values,
# especially more than an hour or so, can lead to trouble as the data in
# the cache does not match up with the actual data anymore
cache-min-ttl: 300
cache-max-ttl: 86400
# Have unbound attempt to serve old responses from cache with a TTL of 0 in
# the response without waiting for the actual resolution to finish. The
# actual resolution answer ends up in the cache later on.
serve-expired: yes
# Harden against algorithm downgrade when multiple algorithms are
# advertised in the DS record.
harden-algo-downgrade: yes
# Ignore very small EDNS buffer sizes from queries.
harden-short-bufsize: yes
# Refuse id.server and hostname.bind queries
hide-identity: yes
# Report this identity rather than the hostname of the server.
identity: "Server"
# Refuse version.server and version.bind queries
hide-version: yes
# Prevent the unbound server from forking into the background as a daemon
do-daemonize: no
# Number of bytes size of the aggressive negative cache.
neg-cache-size: 4M
# Send minimum amount of information to upstream servers to enhance privacy
qname-minimisation: yes
# Deny queries of type ANY with an empty response.
# Works only on version 1.8 and above
deny-any: yes
# Do no insert authority/additional sections into response messages when
# those sections are not required. This reduces response size
# significantly, and may avoid TCP fallback for some responses. This may
# cause a slight speedup
minimal-responses: yes
# Perform prefetching of close to expired message cache entries
# This only applies to domains that have been frequently queried
# This flag updates the cached domains
prefetch: yes
# Fetch the DNSKEYs earlier in the validation process, when a DS record is
# encountered. This lowers the latency of requests at the expense of little
# more CPU usage.
prefetch-key: yes
# One thread should be sufficient, can be increased on beefy machines. In reality for
# most users running on small networks or on a single machine, it should be unnecessary
# to seek performance enhancement by increasing num-threads above 1.
num-threads: 1
# more cache memory. rrset-cache-size should twice what msg-cache-size is.
msg-cache-size: 50m
rrset-cache-size: 100m
# Faster UDP with multithreading (only on Linux).
so-reuseport: yes
# Ensure kernel buffer is large enough to not lose messages in traffix spikes
so-rcvbuf: 4m
so-sndbuf: 4m
# Set the total number of unwanted replies to keep track of in every thread.
# When it reaches the threshold, a defensive action of clearing the rrset
# and message caches is taken, hopefully flushing away any poison.
# Unbound suggests a value of 10 million.
unwanted-reply-threshold: 100000
# Minimize logs
# Do not print one line per query to the log
log-queries: no
# Do not print one line per reply to the log
log-replies: no
# Do not print log lines that say why queries return SERVFAIL to clients
log-servfail: no
# Do not print log lines to inform about local zone actions
log-local-actions: no
# Do not print log lines that say why queries return SERVFAIL to clients
logfile: /dev/null
# Ensure privacy of local IP ranges
private-address: 192.168.0.0/16
private-address: 169.254.0.0/16
private-address: 172.16.0.0/12
private-address: 10.0.0.0/8
private-address: fd00::/8
private-address: fe80::/10
# CLOUDFLARE SETTINGS
server:
tls-cert-bundle: /etc/ssl/certs/ca-certificates.crt
forward-zone:
name: "."
forward-tls-upstream: yes
# Cloudflare DNS
forward-addr: 2606:4700:4700::1111@853#cloudflare-dns.com
forward-addr: 1.1.1.1@853#cloudflare-dns.com
forward-addr: 2606:4700:4700::1001@853#cloudflare-dns.com
forward-addr: 1.0.0.1@853#cloudflare-dns.com
# ADBLOCKING
server:
local-zone: "doubleclick.net" static
local-zone: "googlesyndication.com" static
local-zone: "googleadservices.com" static
local-zone: "google-analytics.com" static
local-zone: "ads.youtube.com" static
local-zone: "adserver.yahoo.com" static
local-zone: "ad-mediation.tuanguwen.com" static
local-zone: "ad.adsrvr.org" static
local-zone: "ad.doubleclick.net" static
local-zone: "ad.lkqd.net" static
local-zone: "adc-ad-assets.adtilt.com" static
local-zone: "admarvel-d.openx.net" static
local-zone: "admediator.unityads.unity3d.com" static
local-zone: "adproxy.fyber.com" static
local-zone: "ads-roularta.adhese.com" static
local-zone: "ads-secure.videohub.tv" static
local-zone: "ads.adadapted.com" static
local-zone: "ads.adecosystems.net" static
local-zone: "ads.admarvel.com" static
local-zone: "ads.api.vungle.com" static
local-zone: "ads.flurry.com" static
local-zone: "ads.heyzap.com" static
local-zone: "ads.mopub.com" static
local-zone: "ads.nexage.com" static
local-zone: "ads.superawesome.tv" static
local-zone: "adtrack.king.com" static
local-zone: "adwatch.appodeal.com" static
local-zone: "amazon-adsystem.com" static
local-zone: "adcolony.com" static
local-zone: "api.salmonads.com" static
local-zone: "app.adjust.com" static
local-zone: "init.supersonicads.com" static
local-zone: "live.chartboost.com" static
local-zone: "marketing-ssl.upsight-api.com" static
local-zone: "track.appsflyer.com" static
local-zone: "ws.tapjoyads.com" static
local-zone: "telemetry.microsoft.com" static
local-zone: "data.microsoft.com" static
Je viens de suivre ta procédure.
Puis j'ai réalisé les deux commandes service unbound restart
Même erreur.
Dans les détails via la commande : systemctl status unbound.service
`● unbound.service - Unbound DNS server
Loaded: loaded (/lib/systemd/system/unbound.service; enabled; vendor preset: enabled)
Active: failed (Result: exit-code) since Fri 2022-03-11 00:54:22 CET; 1min 29s ago
Docs: man:unbound(8)
Process: 1047915 ExecStartPre=/usr/lib/unbound/package-helper chroot_setup (code=exited, status=0/SUCCESS)
Process: 1047918 ExecStartPre=/usr/lib/unbound/package-helper root_trust_anchor_update (code=exited, status=0/SUCCESS)
Process: 1047921 ExecStart=/usr/sbin/unbound -d -p $DAEMON_OPTS (code=exited, status=1/FAILURE)
Process: 1047922 ExecStopPost=/usr/lib/unbound/package-helper chroot_teardown (code=exited, status=0/SUCCESS)
Main PID: 1047921 (code=exited, status=1/FAILURE)
CPU: 23ms
Mar 11 00:54:22 ns336435 systemd[1]: unbound.service: Scheduled restart job, restart counter is at 5.
Mar 11 00:54:22 ns336435 systemd[1]: Stopped Unbound DNS server.
Mar 11 00:54:22 ns336435 systemd[1]: unbound.service: Start request repeated too quickly.
Mar 11 00:54:22 ns336435 systemd[1]: unbound.service: Failed with result 'exit-code'.
Mar 11 00:54:22 ns336435 systemd[1]: Failed to start Unbound DNS server.
root@ns336435:/etc/unbound#`
Hello Matt, je viens aux nouvelles, si tu avais pu jeter un œil ?
Merci à toi.
Hello,
J'ai aucune idée de pourquoi ton unbound démarre pas.
Je vais regarder tes logs ce soir de près.
- Modifié
Salut,
j'ai résolu le problème précédent en réinstallant.
cependant j'ai un autre soucis ^^ quand je choisis dans serveur DNS l'interface wg0, il me dit:
AdGuard Home ne peut pas le configurer automatiquement pour cette interface réseau. Veuillez rechercher une instruction sur la façon de procéder manuellement.
étant sur un vps, je suppose qu'elle est static donc comment résoudre le problème ou je peux continuer ?
edit: j'ai continué et je pense que c'est pas bon pourtant j'ai bien vérifié les étapes...
j'ai défnis les dns sur mon pc windows 1.1.1.1 et 1.0.0.1 et voici ce que j'obtiens:
Connected to 1.1.1.1 Yes
Using DNS over HTTPS (DoH) No
Using DNS over TLS (DoT) No
Using DNS over WARP No
AS Name Cloudflare
AS Number 13335
Cloudflare Data Center CDG
Connectivity to Resolver IP Addresses
1.1.1.1 Yes
1.0.0.1 Yes
2606:4700:4700::1111 No
2606:4700:4700::1001 Nodig -t -A google.fr
;; Warning, ignoring invalid type -A
; <<>> DiG 9.16.27-Debian <<>> -t -A google.fr
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 25886
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;google.fr. IN A
;; ANSWER SECTION:
google.fr. 300 IN A 216.58.201.227
;; Query time: 8 msec
;; SERVER: 194.9.173.89#53(194.9.173.89)
;; WHEN: Mon May 23 18:41:17 CEST 2022
;; MSG SIZE rcvd: 54unbound est bien démarré et activé
May 23 18:34:07 domain.eu unbound[183560]: [1653323647] unbound[183560:0] warning: so-rcvbuf 4194304 was not granted. Got 425984. To fix: start with root permissions(linux) or sysctl >
May 23 18:34:07 domain.eu unbound[183560]: [1653323647] unbound[183560:0] warning: so-sndbuf 4194304 was not granted. Got 425984. To fix: start with root permissions(linux) or sysctl >
May 23 18:34:07 domain.eu systemd[1]: Started Unbound DNS server.
pourtant j'ai installé en root :x (edit: lié à la mémoire, j'ai donc ajouté: net.core.rmem_default = 31457280
net.core.rmem_max = 12582912
net.core.wmem_default = 31457280
net.core.wmem_max = 12582912
)
cloudflared pareil:
● cloudflared.service - Cloudflare with DNS over HTTPS proxy
Loaded: loaded (/lib/systemd/system/cloudflared.service; enabled; vendor preset: enabled)
Active: active (running) since Mon 2022-05-23 18:28:47 CEST; 18min ago
Main PID: 183505 (cloudflared)
Tasks: 8 (limit: 4695)
Memory: 15.7M
CPU: 563ms
CGroup: /system.slice/cloudflared.service
└─183505 /usr/local/bin/cloudflared proxy-dns --port 5053 --upstream https://1.1.1.1/dns-query
May 23 18:28:47 domain.eu systemd[1]: Started Cloudflare with DNS over HTTPS proxy.
May 23 18:28:47 domain.eu cloudflared[183505]: 2022-05-23T16:28:47Z INF Adding DNS upstream url=https://1.1.1.1/dns-query
May 23 18:28:47 domain.eu cloudflared[183505]: 2022-05-23T16:28:47Z INF Starting metrics server on 127.0.0.1:39419/metrics
May 23 18:28:47 domain.eu cloudflared[183505]: 2022-05-23T16:28:47Z INF Starting DNS over HTTPS proxy server address=dns://localhost:5053
24/05/2022: Tout est réglé après une nuit de sommeil ^^ Merci pour ce magnifique tutoriel!
Cordialement,
Bonjour,
Un petit message à @MattProd car c'est vraiment un super taff ce tutorial.
C'est exactement ce que je voulais faire , mais réellement j'y connais pas grand chose en infra et j'aurais été incapable de le faire. J'avais fais une tentative, fin 2021/de 2022 sans succes. J'ai recommencé ce mois ci et ca marche nikkel !
C'est incroyable.
J'ai du coup un petit vps avec toute cette installation. Et j'ai redirigé tout mon traffic de chez moi dessus.
J'ai plusieurs sites qui bloque l'utilisation de vpn mais autrement c'est vraiment top !
En grand merci encore, tu as fait un heureux !
bonjour à tous,
le tuto est vraiment trés précis et complet mais j'ai du me planter quelque part.....
je n'arrive pas à me connecter via mon smartphone sur https://1.1.1.1/help.
je suis sous ubuntu
merci d'avance pour votre aide
jerome si tu vas sur un site tel que https://ip.mn83.fr est-ce que tu vois l'ip de ton vpn ou celle de ton fai ?
Il nous faudra chercher à tatillon sans avoir plus de détails.
Matt